By Kevin King
(This is a 2-part article. You can find Part 1 here.)
In a very real sense, in World War II, many battles—and perhaps the course of the war—were changed by the science of cryptography. Some examples are the cracking of Germany’s Enigma code, the Japanese “Purple,” and also JN-25 which led to the allied victory at Midway.[i]
Nowadays, encryption attackers have a vast assortment of methods to steal our precious information, from massive data centers sporting thousands of processor cores and terabytes of RAM, to the nascent explosive advance of quantum computing.
But frankly, all you usually need is a laptop.
That’s right, it can be fairly easy to capture data that is inadequately protected. Here are some headlines from just this month:
- “GDPR Compliance Site Leaks Git Data, Passwords”
- “Nintendo data breach reportedly caused by credential stuffing”
- “Nearly 25,000 email addresses and passwords allegedly from NIH, WHO, Gates Foundation and others are dump[ed]”
- “500,000 Hacked Zoom Accounts Given Away For Free On The Dark Web”
- “French Newspaper Le Figaro Leaks 7.4 Billion Records”
I could go on. My search for a month’s worth of news articles netted me 22 pages of examples[ii]. And if your practice hasn’t been hit so far, well, it's just because they haven’t given you a good look yet. So, let’s just avoid that eventuality and protect the data that we hold so dear.
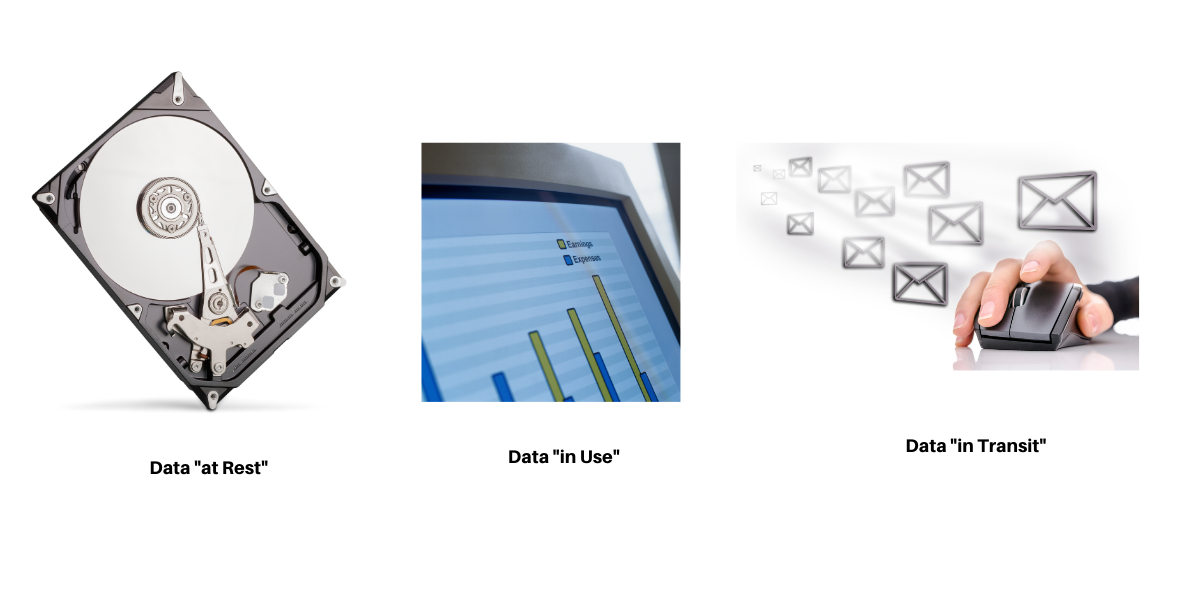
There are only three items that need protecting:
- Data at rest
- Data in motion
- Data in use
Data At Rest is “inactive data that is stored physically in any digital form.[iii]” This can be a spreadsheet, database, or any data stored on a hard disk, whereas Data In Motion is data that is being transmitted over a medium, such as an ethernet cable or wirelessly. Lastly, Data in Use is what you see right now: The apps and data that you are using while you are looking at your computer. It is stored in active computer memory (RAM).
The table below shows how to protect each type of data:
| Data Type | Protection Method | Common Applications |
|---|---|---|
| At Rest | Identity Management Encryption |
Active Directory BitLocker |
| In Motion | VPN | Sonicwall SSL VPN |
| In Use | Identity Management |
Active Directory 2 Factor Authentication |
Do This Today
- Make sure that every workstation, laptop, and server has an enterprise login like the one through Active Directory (using 2-factors where possible e.g. login AND fingerprint)
- Make sure your laptop and desktops are using “whole disk” encryption, like BitLocker or Check Point Full Disk Encryption. Be sure that the SD cards on your mobile devices are encrypted.
- Use a VPN for communications to and from your practice. Always check with your firewall vendor to see if they offer VPN. Most do.
Don’t let the problems we’ve had since WWII catch up to you as you see your data stolen. Use these techniques to protect it now.

Kevin King is a Certified Security Analyst, and holds many IT and Cybersecurity Certifications. He teaches ethical hacking and does security and infrastructure consulting.




